In three days, the Ether House will embrace these major changes
The nine major EIP proposals for the upgrade of Fusaka are being studied in hard copy。

The nine major EIP proposals for the upgrade of Fusaka are being studied in hard copy。

Original fromSaul Sojitra
Compile Odaily Daily Planet Golem()@web3_golemI'm not sure
The Fusaka hard-drive, which is scheduled to be activated on December 3, 2025, is another major upgrade of the network after the Taifung Pectra, marking another important step in the expansion of the encryption giant。
Pectra upgrade EIP focuses on upgrading performance, security and developer tools. The EIP for Fusaka upgrade focuses on expansion, code updating and implementation security。
PeerDAS (EIP-7594) enhanced data availability by allowing nodes to validate Blob without downloading all data. Various upgrades have also enhanced the security of implementation, including restrictions on ModExp (EIP-7823), transaction restrictions on Gas limits (EIP-7825) and updating of ModExp Gas costs (EIP-7883). This Fusaka upgrade has also improved block generation through the Affirmative Prospecters Forwarding Mechanism (EIP-7917) and maintained the stability of Blob costs (EIP-7918) by setting “reserved prices” linked to implementation costs。
Other enhancements include limiting the size of blocks in RLP format (EIP-7934), adding new CLZ codes to speed up bit operations (EIP-7939) and introducing secp256r1 pre-compilation (EIP-7951) to better accommodate modern passwords and hardware security keys。
Fusaka is the combination name of Fulu (executive level) and Osaka (consensus level). It represents another step towards a highly scalable and data-rich future in which Layer 2 Rollup can run at lower cost and faster speed。
This article will provide an in-depth analysis of the nine core EIP proposals for the Fusaka hard-drive。
This proposal is needed because the network wants to provide users (especially Rollup users) with greater data availability。
However, under the current EIP-4844 design, each node still needs to download a large amount of blob data to verify its release. This raises the issue of extension, as if all data had to be downloaded at all nodes, the bandwidth and hardware requirements of the network would increase and decentrization would be affected. In order to address this problem, an approach is needed to allow nodes to confirm the availability of data without downloading all data。
DATA USABILITY SAMPLING (DAS) ADDRESSES THIS PROBLEM BY ALLOWING ONLY A SMALL AMOUNT OF RANDOM DATA TO BE CHECKED AT NODES。
But it also requires a DAS approach that is compatible with the existing Gosip network and does not impose a heavy computing burden on block producers. PeerDAS was created to meet these needs and to safely increase blob throughput while keeping nodal demand low。
PeerDAS is a network system that allows nodes to download only a small number of data clips to verify that the complete data has been released。Node does not need to download all data, but rather uses the regular Gossip network to share data, discover which nodes hold part of the data and request only small samples as required. The core idea is that by downloading only a random fraction of the data section, the node can still be convinced of the existence of the entire data section. For example, the node may only download about 1/8 data instead of the full 256 KB data clips - as many nodes sample different parts, any missing data will be quickly discovered。
In order to achieve sampling, PeerDAS uses a basic redacting code to expand each of the data segments in EIP-4844。Redressing is a technique for adding additional redundant data, and even the absence of certain data segments restores the original data — similar to a puzzle that can be completed even if several pieces are lost。
blob becomes a line containing raw data and some additional coding data so that subsequent data can be rebuilt. This line is then divided into blocks called " Cells " , which are the smallest validation units associated with KZG commitments. All rows are then reorganized into columns, each of which contains cells at the same location from all rows. Each column is assigned to a specific Gossip subnet。
Node is responsible for storing certain columns according to its node ID and sampling some columns from the peer node at each time interval. If a node collects at least 50% of the columns, it can completely rebuild the data. If less than 50% of the column is collected, it is required to request the missing column from the peer node. This ensures that if data are actually released, they can always be rebuilt. In short, if there are a total of 64 columns, only about 32 columns are required for a single node to rebuild the whole blob. It keeps its own columns and downloads columns from peer nodes. As long as half of the columns in the network exist, the node can rebuild all content, even if some columns are missing。
In addition, EIP-7594 introduced an important rule: no transaction can contain more than six blobs。this restriction must be enforced during transaction validation, gossip dissemination, block creation and block processing. this helps to reduce the extremes in which individual transactions result in overloading of the blob system。
PeerDAS adds a function called "unit KZG certificate". Module KZG attests that KZG promise does match a particular cell (a small unit) in blob. This allows nodes to download only the cell they want to sample. Access to complete blobs is essential for data availability sampling, subject to data integrity。
However, the cost of generating all these units proved to be high. Block producers need to compute these certificates over and over again for many blobs, which makes them too slow. However, the cost of certification is very low, and therefore the EIP-7594 requires the manufacturer of the blob transaction to pre-generated all the unit certificates and to include them in the trade packaging。
For this reason, the transaction Gossip uses a modified packaging:
rlp([tx_payload_body, wrapper_version, blobs, committees, cell_proofs])
In the new packaging, the cell_proofs is a list containing all the certificates for each unit of each blob (e.g. [cell_proof_0, cell_proof_1,...]). Other fields tx_payload_body, blues and committees are identical to EIP-4844. The difference is that the original individual "proofs " field was removed and replaced with a new cell_proofs list, and a field named wrapper_version was added to indicate the packaging format currently used。
PeerDAS enables the Ether Workshop to increase data availability without increasing the workload of its nodesI don't know. Today, a node only needs to sample about 1/8 of total data. In the future, the ratio may even fall to 1/16 or 1/32, thereby increasing the expansionability of the Taicha. The system is working well because each node has numerous reciprocal nodes, so that if a node cannot provide the required data, the node can request other nodes. This naturally creates redundancy mechanisms and improves security, while nodes can choose to store data in excess of actual needs, which further enhances network security。
Validation nodes assume more responsibility than ordinary whole nodes. Because the validation node itself runs more efficient hardware, PeerDAS will assign the corresponding data hosting load to it based on the total number of authentication nodes. This ensures that there is always a stable nodal group that can be used to store and share more data, thereby increasing the reliability of the network. In short, if there were 900,000 certification nodes, each certification node could be allocated a small percentage of total data for storage and services. With stronger machines at the validation nodes, the network can trust them to ensure data availability。
PeerDAS uses a column sample instead of a sample, as this would greatly simplify data reconstruction. If the entire line (whole blob) is sampled at node, there is a need to create an additional “extension blob” that would otherwise not exist, which would slow down the pace of block producers。
by sampling, the node can pre-preparate additional line data and the transaction sender (rather than block producers) calculates the necessary proof. this will maintain the speed and efficiency with which blocks are created. for example, assume that a blob is a 4x4 cell grid. line sampling means that all four cells are removed from a row, but some extension lines are not ready, so block producers must produce them on site; column sampling takes a cell from each row (each column) and rebuilds the extra cells needed to be pre-prepared so that nodes can validate data without slowing down the production of blocks。
EIP-7594 IS FULLY COMPATIBLE WITH EIP-4844 AND THEREFORE DOES NOT UNDERMINE ANY OF THE EXISTING FUNCTIONS OF THE ETHER HOUSE. ALL TEST AND DETAILED RULES ARE INCLUDED IN THE CONSENSUS AND IMPLEMENTATION NORMS。
THE MAIN SECURITY RISK FOR ANY DAS SYSTEM IS “DATA CONCEALMENT ATTACK”, I.E. BLOCK PRODUCERS PRETEND TO HAVE DATA AVAILABLE, BUT IN FACT HIDE SOME DATA。PeerDAS prevents this by using random sampling: nodes check for random parts of data. The more nodes are sampled, the harder it is for the attackers to cheat. EIP-7594 even provides a formula that can be calculated on the basis of the total number of nodes (n), the total number of samples (m) and the sample number of each node (k). PeerDAS is considered safe because of the extremely low probability of success of the attack on the Internet of the Etherman, which has about 10,000 nodes。

THE NEED FOR THIS PROPOSAL IS THAT THE CURRENT MODEXP PRE-COMPILATION MECHANISM OF THE ETA HAS LED TO MANY CONSENSUS GAPS OVER THE YEARS. MOST OF THESE LOOPHOLES STEM FROM THE FACT THAT MODEXP ALLOWS EXTREMELY LARGE AND UNREALISTIC AMOUNTS OF DATA TO BE ENTERED, MAKING IT NECESSARY FOR THE CLIENT TO DEAL WITH NUMEROUS ANOMALIES。
Since each node has to process all inputs provided by the transaction, the absence of a ceiling makes MODEXP more difficult to test, more prone to error and easier to perform differently on different clients. Excessive input data also make the Gas cost formula difficult to predict, as it is difficult to price when data volumes can grow indefinitely. These problems also make it difficult to replace MODEXP with an EVM level code in the future using tools such as EVMMAX, because without fixed limits the developers cannot create safe and optimized implementation paths。
IN ORDER TO REDUCE THESE PROBLEMS AND IMPROVE THE STABILITY OF THE ETHER WORKSHOP, EIP-7823 HAS ADDED A STRICT CAP ON THE VOLUME OF MODEXP INPUT DATA, THUS MAKING THE PRE-COMPILATION PROCESS SAFER, EASIER TO TEST AND MORE PREDICTABLE。
EIP-7823 INTRODUCES A SIMPLE RULE: ALL THREE LENGTH FIELDS (BASIC, INDEX AND MODEL) USED BY MODEXP MUST BE LESS THAN THE EQUIVALENT OF 8192 BITS, OR 1024 BYTES。MODEXP input follows the format defined in EIP-198:
FOR EXAMPLE, IF SOMEONE TRIES TO PROVIDE A 2000 BYTE BASE FIGURE, THE CALL WILL FAIL BEFORE ANY WORK BEGINS. THESE LIMITATIONS CAN STILL SATISFY ALL PRACTICAL APPLICATIONS. RSA AUTHENTICATION USUALLY USES THE SAME KEY LENGTH AS 1024, 2048 OR 4096, WHICH ARE WITHIN THE NEW LIMIT. AN ELLIPTICAL CURVE OPERATES WITH A SMALLER INPUT SIZE, USUALLY LESS THAN 384 BITS, AND IS THEREFORE UNAFFECTED。
THESE NEW CONSTRAINTS ALSO CONTRIBUTE TO FUTURE ESCALATION. IF THE FUTURE EVMMAX REWRITES MODEXP AS AN EVM CODE, THE DEVELOPER CAN ADD AN OPTIMISED PATH TO THE COMMON INPUT SIZE (E. G. 256, 381 OR 2048) AND USE SLOW EXIT SOLUTIONS FOR RARE CASES. BY FIXING THE MAXIMUM INPUT SIZE, THE DEVELOPERS CAN EVEN ADD SPECIAL TREATMENTS TO VERY COMMON MODULES. PREVIOUSLY, THESE COULD NOT BE ACHIEVED BECAUSE OF THE UNLIMITED SIZE OF THE INPUT, THE SIZE OF THE DESIGN SPACE AND THE DIFFICULTY OF MANAGING IT SAFELY。
IN ORDER TO CONFIRM THAT THIS CHANGE WILL NOT DISRUPT PAST TRANSACTIONS, THE AUTHOR ANALYSES ALL MODEXP USAGES FROM BLOCKS 5,472,266 (20 APRIL 2018) TO BLOCKS 21,,550,926 (4 JANUARY 2025). THE RESULTS SHOW THAT NONE OF THE SUCCESSFUL MODEXP CALLS IN HISTORY USED MORE THAN 513 BYTES, WELL BELOW THE NEW 1024 BYTES LIMIT. MOST ACTUAL CALLS USE SMALLER LENGTHS, SUCH AS 32 BYTES, 128 BYTES OR 256 BYTES。
There are some invalid or corrupt calls, such as empty input, filled with duplicate bytes, and a very large but invalid input. These acts, which are referred to under the new restrictions, are also invalid, as they themselves are invalid。SO, WHILE EIP-7823 IS A MAJOR TECHNICAL CHANGE, IT DOES NOT ACTUALLY CHANGE THE OUTCOME OF ANY PAST TRANSACTIONS。
FROM A SECURITY POINT OF VIEW, REDUCING THE PERMITTED INPUT SIZE DOES NOT POSE NEW RISKS. INSTEAD, IT ELIMINATES UNNECESSARY EXTREMES THAT HAD PREVIOUSLY LED TO ERRORS AND INCONSISTENCIES BETWEEN CLIENTS. BY LIMITING MODEXP INPUT TO A REASONABLE SIZE, EIP-7823 MAKES THE SYSTEM MORE PREDICTABLE, REDUCES ODD EXTREMES AND REDUCES THE PROBABILITY OF ERRORS BETWEEN DIFFERENT REALIZATIONS. THESE CONSTRAINTS ALSO HELP PREPARE THE SYSTEM FOR A SMOOTHER TRANSITION IF FUTURE UPGRADES (E.G. EVMMAX) INTRODUCE AN OPTIMAL IMPLEMENTATION PATH。
It is true that this proposal is also needed in the Ether Workshop, as a single transaction can currently consume the gas ceiling of the entire block。
This could create several problems: a transaction could consume most of the resources of blocks, leading to slow delays in attacks such as DoS; costly Gas operations would add up too quickly to the status of the Taifeng; and the validation of blocks would become slower and nodes would be difficult to keep up with。
If one user submits a large transaction that consumes almost all Gas (e.g. a transaction that consumes 38 million Gas out of a block of 40 million Gas), other ordinary transactions cannot be placed in the block, and each node must take extra time to verify the block. This threatens the stability and decentrization of the network, as slower validation means that weaker nodes will lag behind. To address this problem, the Ether Workshop needs a secure Gas cap that limits the number of Gass that can be used for a single transaction, thereby making block loads more predictable, reducing the risk of DoS attacks and balancing loads at nodes。
EIP-7825 introduces a mandatory rule that no transaction may exceed 16,777,216 (224)。This is the upper limit at the level of the agreement, meaning that it applies to all links: the user sends the transaction, the transaction is checked in the trading pool and the certifying officer packs the transaction into the block. If someone sends a Gas cap above this value, the client must immediately reject the transaction and return an error similar to MAX_GAS_LIMIT_EXCEEDED。
This upper limit is fully independent of the upper limit of block Gas. For example, even if the size of the block Gas ceiling was 40 million, the consumption of any single transaction would not exceed 16.7 million. The aim is to ensure that each block can accommodate multiple transactions, rather than allowing a single transaction to occupy the entire block。
To better understand this, it is assumed that a block can accommodate 40 million Gas. Without this cap, someone may send a transaction that consumes 35 million to 40 million Gas. The deal monopolized the block, leaving no room for other transactions, just as one person wrapped the entire bus and no one else could get on the bus, and the new 16.7 million Gas cap would naturally accommodate multiple transactions and thus avoid such abuses。
The proposal also sets out specific requirements for the customer to verify the transaction. If the transaction exceeds 16,777,216, the trading pool must reject the transaction, which means that the transaction will not even enter the queue. During the block validation process, if the block contains transactions exceeding the ceiling, the block itself must be rejected。
Option 16,777,216 (224) this figure is because it is a clear 2-sided sub-border, easy to achieve and still large enough to handle most of the actual transactions。For example, smart contract deployment, complex DeFi interactive or multistep contract calls. This value is about half the size of typical blocks, which means that even the most complex transactions can easily be contained within this limit。
This EIP also maintains compatibility with the existing Gas mechanism. Most users will not notice this change because almost all existing transactions consume far less than 16 million Gas. The certifiers and block creators can still create blocks that total the Gas above 16.7 million, as long as each transaction complies with the new ceiling。
The only transactions affected were previous attempts to use super-maximum transactions beyond new restrictions. These transactions now have to be split into smaller operations, similar to uploading a very large document into two smaller ones. Technically, this change is not downward compatible with these rare extreme transactions, but it is expected that very few users will be affected。
In terms of safety, the Gas ceiling has made the Ether House more resistant to Gas-based DoS attacks, as the attackers are no longer in a position to force the certifying officers to deal with super-trading transactions。It also helps to keep block validation time predictable, making it easier to keep the nodes synchronized. The main extreme is that a small number of very large contractual deployments may not meet the ceiling requirements and need to be redesigned or split into multiple deployment steps。
Overall, EIP-7825 is aimed at strengthening the network against misuse, maintaining a reasonable demand for nodes, improving equity in the use of block space and ensuring that the block chain remains fast and stable as the Gas ceiling rises。
The reason for the need for this proposal is that the price of the ModExp pre-compilation (for modelling operations) has been low compared to the resources actually consumed。
In some cases, the calculations required for the ModExp operation far exceed the costs currently paid by the user. This mismatch poses risks: if complex ModExp calls are too low, they may become bottlenecks, making it difficult for the network to safely raise the Gas ceiling. Because block producers may be forced to handle extremely heavy operations at very low cost。
In order to address this problem, it is necessary to adjust the ModExp pricing formula so that Gas consumption accurately reflects the actual workload performed by the client. SoEIP-7883 introduced new rules that increased the minimum Gas cost, raised the total Gas cost and made the operation of the larger input volume (especially index, base or model over 32 bytes) more expensive, thereby matching the Gas pricing with the actual calculation required。
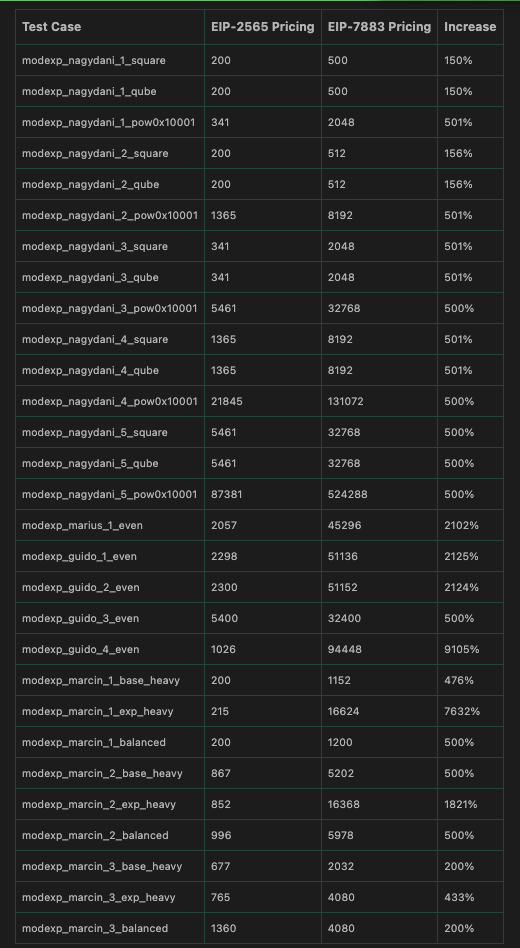
The proposal raised costs through several important aspects, thereby modifying the ModExp pricing algorithm originally defined in EIP-2565。
First, the lowest Gas consumption was raised from 200 to 500, and total Gas consumption was no longer divided by three, meaning that total Gas consumption actually tripled. For example, if a previous ModExp call required the consumption of 1200 gas, under the new formula, it would now require the consumption of approximately 3,600 gas。
SECOND, THE CALCULATION COST OF AN INDEX GREATER THAN 32 BYTES DOUBLED, AS THE MULTIPLIER INCREASED FROM 8 TO 16. FOR EXAMPLE, IF THE INDEX LENGTH IS 40 BYTES, EIP-2565 INCREASES THE NUMBER OF ITERATIVES BY 8 X (40 − 32) = 64, WHILE EIP-7883 NOW USES 16 X (40 − 32) = 128, DOUBLING COSTS。
Third, pricing now assumes that the minimum base/module size is 32 bytes and that when these values exceed 32 bytes, the calculated cost increases dramatically. For example, if the number of modules is 64 bytes, the new rule applies double complexity (2 x words2) rather than a simpler formula before, thus reflecting the actual cost of large-scale operations. Together, these changes ensure that small ModExp accounts pay a reasonable minimum cost and that the costs of large, complex operations are appropriately adjusted to their size。
The proposal defines a new Gas computing function and updates the complexity and iterative rules. Multiplication complexity now uses default 16 for cases where the base/module length does not exceed 32 bytes, while for larger inputs the more complex formula 2 x words2, where "words" refers to the number of 8 bytes. The number of iterations has also been updated so that 32 bytes or smaller indices use their bit length to determine complexity, while an index greater than 32 bytes increases the Gas punishment。
This ensures that the real-cost hyper-index now has higher Gas costs. It is important that the minimum Gas cost of return is imposed at 500 instead of the previous 200, which makes even the simplest ModExp call more reasonable。
These price increases were motivated by baseline tests, which showed that in many cases ModExp pre-compiled prices were significantly lower。The revised formula increases the costs of small operations by 150 per cent, typical operations by approximately 200 per cent, and large or unbalanced operations by more than a factor of 80, depending on the size of the index, base or modelI don't know。
The aim is not to change ModExp ' s working methods, but to ensure that it does not threaten the stability of the network or impede the future rise of the Gas cap of the block, even in the extreme case of maximum resource consumption. As EIP-7883 changed the number of Gas required for ModExp, it was not re-compatible, but Gas heavy pricing has occurred repeatedly in the Ethern and has been fully understood。
The results of the tests showed that the increase in Gas costs was significant at this time. About 99.69 per cent of history ModExp calls now require either 500 Gas (previously 200 Gas) or three times the previous price. However, the cost of some of the high load tests used by Gas has increased even more. For example, in a “index-intensive” test, Gas consumption jumped from 215 to 16,624, an increase of approximately 76 times, because it is now more rational to price a large index。
In terms of safety, the proposal would not introduce a new route of attack or reduce the cost of any calculation. Instead, it focuses on the prevention of an important risk: the under-pricing ModExp operation may allow the attackers to fill the block with extremely heavy calculations at very low cost. The only possible disadvantage is that some ModExp operations may be overpriced, but this is far better than the current problem of underpricing. The proposal does not introduce any interface changes or new features, so the existing arithmetical behaviour and test vector remain valid。
This proposal is needed in the Ether Workshop because the deployment of the proponents of the next epoch network cannot be fully predicted. Even with RANDAO seeds known in N epoch N +1 epoch, the actual list of proponents could be changed by updating the active balance (EB) in N epoch。
These EB changes may come from forfeiture, punishment, incentives exceeding 1 ETH, certificationer consolidation or new deposits, especially after EIP-7251 has increased the maximum effective balance to above 32 ETH. Such uncertainty poses problems for those systems that rely on knowing in advance the next proponent (e.g., based on pre-confirmation agreements), which require a stable and predictable timetable for their smooth operation. A certifier may even try to “brush” or manipulate its effective balance to influence the next epoch proponent。
As a result of these problems, an approach is needed to make the timetable of the proponent fully established in several future epochs, so that it is not altered by last-minute EB updates and is easily accessible at the application level。
In order to achieve this, EIP-7917 introduced a certainty proponent forward-looking mechanism whereby the next MIN_SEED_LOOKAHEAD + 1 epoch schedule is calculated and stored in advance at the beginning of each epoch。in short, the beacon status now contains a list called `prosoperer_lookahead ' , which always covers the proponents of two full cycles (a total of 64 time slots)。
For example, when epoch N started, the list already included the proponents of each time slot in epoch N and epoch N+1. Then, when the network enters the N+1 cycle, the list moves forward: remove the N-cycle proposer entry, move the N+1 entry of the cycle to the front of the list and add a new proposer entry for N+2 at the end of the list. This allows movement movements to be fixed, predictable and accessible directly to clients without having to recalculate the proponent at each time slot。
to keep up-to-date, the list moves forward at each epoch border: removes the previous epoch data and calculates and adds to the list the next set of new proponents for epoch. the process uses the same seed and effective balance rules as before, but movement control is now calculated earlier, thus avoiding the impact of changes in the effective balance once seeds are identified. the first block after the fork will also fill the entire forward range to ensure that all future epochs have the correct initial movement。
Assuming that each epoch has 8 slots instead of 32 (for simplification). Without this EIP, while you know the seed of the 6th epoch during the 5th epoch, the actual proposer of the 6th epoch slot is likely to change if the certifier is disallowed or rewarded enough to change its valid balance during the 5th epoch period. With EIP-7917, ETA precalculated all the proponents of the 5th, 6th and 7th epoch at the start of the 5th epoch and stored them sequentially in `prospers_lookahead ' . So even if the balance changes at the end of the fifth epoch, the list of 6 epoch proponents remains fixed and predictable。
EIP-7917 repaired long-standing deficiencies in beacon chain design. It ensures that the future epoch certifier selection cannot be changed once the previous epoch RANDAO is available. This also prevents the `effective balance brushing', i.e. the certifying officer, after seeing RANDAO, attempts to adjust its balance to influence the list of proponents of the next epoch. The certainty forward-looking mechanism eliminates the entire attack vector and greatly simplifys security analysis. It also enables the consensus client to know in advance who will propose the forthcoming block, which will help to achieve and allow the application layer to easily validate the proposer ' s calendar through Merkel, the root beacon。
Before this proposal, the client only calculates the proponent of the current gap. With EIP-7917, they will now calculate the list of proponents of the next epoch all time horizons once in every epoch conversion. This would add a small amount of work, but the index of the proposer would be very light and would mainly involve sampling the certification list using seeds. However, the client needs to be benchmarked to ensure that this additional calculation does not cause performance problems。
This proposal is needed in the Ether Workshop because the current Blob Cost System (from EIP-4844) will fail when Gas becomes the main cost of Rollup。
Currently, most Rollup pays far more for the execution of Gas (cost of including Blob transactions in blocks) than the actual Blob costs. This poses a problem: even if the Blob base costs are constantly reduced by the utensils, the total cost of Rollup has not actually changed, as the highest cost is still the implementation of Gas. As a result, the Blob base costs will continue to decline until they reach an absolute minimum (1 wei), at which point the agreement will no longer be able to use Blob costs to control demand. Then, when Bloom's usage suddenly rises, it takes a lot of blocks to recover to normal levels. This makes prices unstable and unpredictable for users。
For example, assuming that a Rollup would like to publish its data, it would have to pay about 25,000,000 gwei for execution Gas (approximately 1,000,000 gwei for 25 gwei), the cost of Blob would be only about 200 gwei. This means that the total cost is approximately 25,000,200 gwei, of which almost all costs come from the implementation of Gas, not Blob. If the cost of Blob continues to be reduced in the same way, for example from 200 gwei to 50 gwei, then down to 10 gwei and eventually down to 1 gwei, the total cost will hardly change and remains at 25,000,000 gwei。
EIP-7918 Solve this problem by introducing a minimum “reserved price” based on implementation base costs, thereby preventing too low Blob prices and making Blob pricing in Rollup more stable and predictable。
The core idea of EIP-7918 is simple: Blob should never be priced less than a certain amount of execution costs (known as BLOB_BASE_COST)。the value of calc_execs_blob_gas() is set to 213, which is achieved through minor modifications to the calc_excs_blob_gas() function。
Normally, this function increases or reduces the base cost of the Blob depending on whether the blob gas used in the block is above or below the target value. According to this proposal, if Blob becomes "too low" relative to the execution of Gas, the function will stop deducting the target Blob Gas. This has led to a faster growth of the excess blob gas, thus preventing a further decline in the blob base cost. So, Blob's base cost now has a minimum value equal toBLOB_BASE_COST x base_fee_per_gas ÷ GAS_PER_BLOB。
In order to understand why we need to do this, we can look at Blob's needs. Rollup is concerned about the total costs it pays: implementation costs plus blob costs. If the costs of implementing Gas are very high, for example, 20 gwei, then the total costs will be almost constant even if Blob costs are reduced from 2 gwei to 0.2 gwei. This means that the reduction of the Blob base costs has little impact on demand. In economics, this is called “cost inflexibility”. It creates a situation in which the demand curve is almost vertical: lower prices do not increase demand。
In such cases, the Blob base cost mechanism becomes blind - even if demand does not respond, it continues to reduce prices. This is why the base cost of the blob is often down to 1 gwei. Then, when actual demand increases at a later stage, the agreement takes an hour or more to raise the cost to a reasonable level of almost full blocks. EIP-7918 Solve the problem by establishing reserve prices linked to the implementation of Gas, thus ensuring that Blob costs remain meaningful even if implementation costs prevail。
Another reason for adding this reserved price is that the node requires a lot of extra work to verify the KZG certificate of Blob data. These certificates ensure that the data in Bob are consistent with their commitments. Under EIP-4844, the node only needs to verify a certificate for each Blob at a low cost. However, in EIP-7918, the number of certificates required to be validated is higher. It's all because in EIP-7594 (PeerDAS), the blob is divided into small pieces called cell, each of which has its own proof, which makes the validation work much bigger。
In the long run, EIP-7918 also helps prepare for the future. With advances in technology, the cost of storing and sharing data will naturally decrease, and it is expected that the workshop will allow more Blob data to be stored over time. Blob costs (in ETH) will naturally decline when Blob capacity increases. This is supported by the proposal, as the retention of prices is linked to the execution of Gas prices, rather than a fixed value, so that it can be adjusted to the growth of the network。
With the expansion of Blob space and implementation block space, their price relationship will be balanced. Only in very few cases can retention prices be excessive when Blob capacity is significantly increased at the fare without increasing implementation capacity at Gas. In such cases, the Blob costs may eventually be higher than the actual requirements. However, there are no plans to expand in this way — the Bloom space and the implementation block space are expected to grow simultaneously. The selected value (BLOB_BASE_COST = 213) is therefore considered safe and balanced。
A small detail was needed when the costs of implementing Gas surged. Since the price of Blob depends on the base cost of implementation, a sudden increase in the cost of implementation may temporarily put the cost of Blob in a situation dominated by implementation costs. For example, it is assumed that the implementation of Gas costs suddenly jumped from 20 to 60 gwei within a block. As Blob prices are linked to this value, Blob costs cannot break new and higher levels. If Blob is still in use, its costs will continue to increase normally, but the agreement will not allow it to decline until it increases sufficiently to match higher implementation costs. This means that within several blocks, Blob costs may grow slower than implementation costs. This short delay is harmless — it actually prevents sharp fluctuations in Blob prices and makes the system more stable。
the author also conducted an empirical analysis of actual block trading activities in november 2024 to march 2025 and applied price retention rules. during periods of high implementation costs (on average about 16 gwei), the reserve threshold significantly increased block base costs compared to the old mechanism. during the period of low implementation costs (average of about 1.3 gwei), block costs remained almost constant unless the base cost of blocks was calculated below the reserve price. by comparing thousands of blocks, the author shows that the new mechanism can create more stable pricing while maintaining a natural response to demand. the four-month figure for block costs shows that reserve prices have reduced extreme volatility by preventing block costs from falling to 1 gwei。
As far as safety is concerned, this change will not introduce any risk. The cost of the base block will always be equal to or higher than the unit cost of implementing the BLOB_BASE_COST in Gas. This is safe because the mechanism increases only the minimum cost, and setting price thresholds does not affect the correctness of the agreement. It just ensures healthy economic functioning。
Before EIP-7934, there is no strict ceiling on the size of the RLP coded enforcement blocks. In theory, blocks may be very large if they contain large transactions or very complex data. This raises two main issues: network instability and the risk of denial of services (DoS)。
If the blocks are too large, the time required to download and validate the nodes will be longer, which will slow down their transmission and increase the possibility of temporary branch chains. Worse still, the attackers could deliberately create a very large block to overload the nodes, causing delays or even de-linking them — a typical denial-of-service attack. At the same time, the CL Gossip agreement has refused to spread any block above 10MB, which means that too large an implementation block may not be disseminated in the network, thus creating fragmentation of the chain or disagreement between nodes. In view of these risks, a clear protocol-level rule is needed to prevent excessive size and maintain network stability and security。
EIP-7934 addresses this problem by introducing an agreed-level RLP enforcement block size cap. Maximum allowed block size (MAX_BLONK_SIZE) is set to 10 MiB (10,485,760 bytes), but 2 MiB (2,097,152 bytes) is added on the basis of the Taifeng because beacon blocks also occupy some space (SAFETY_MARGIN)。
This means that the maximum allowed RLP encoded enforcement block size is MAX_RLP_BLONK_SIZE = MAX_BLONK_SIZE-SAFETY_MARGIN. If the encoded block is larger than this limit, the block will be considered invalid and the node must reject it. With this rule, block producers have to check the size of the code of each block they construct, and the certifier has to verify this limitation during the block certification. This size cap is independent of the Gas limit, which means that even if the block is “lower than the Gas limit”, it will still be rejected if it is too large. This ensures that Gas usage and actual byte size limits are observed。
Selecting the upper limit of 10 MiB is intentional because it matches the existing limitations in the Consensus Level Gossip agreement。Any data larger than 10 MiB will not be broadcast online, so this EIP aligns the enforcement with the consensus level limits. This ensures consistency among all components and prevents the effective implementation of the “visibility” of blocks as a result of CL refusal to disseminate。
This change does not comply downward with blocks larger than the new limit, which means that miners and certifyers must update their clients to comply with the rule. However, since megablocks are themselves problematic and not common in practice, their impact is minimal。
In terms of safety, EIP-7934 has significantly enhanced the ability of the Taifang to withstand attacks on DoS at the size of specific blocks by ensuring that no participant is able to create blocks that will paralyze the network。IN SUM, EIP-7934 ADDS AN IMPORTANT SECURITY BORDER, INCREASES STABILITY, HARMONIZES IMPLEMENTATION LOGIC (EL) AND CL BEHAVIOUR, AND PREVENTS MULTIPLE ATTACKS ASSOCIATED WITH THE CREATION AND DISSEMINATION OF MEGABLOCKS。
Before this EIP, the number of zeros leading to 256 bits is calculated using an operation code that the Taifeng does not have. Developer has to use Solidity to manually implement the CLZ function, which requires a large number of offsets and comparisons。
IT'S A BIG PROBLEM, BECAUSE SELF-DEFINED ACHIEVEMENT IS SLOW, COSTLY AND TAKES A LOT OF BYTES, ADDING Gas consumption. For a zero-knowledge certification system, the cost of proof is higher and the cost of proof of right-transfer operations is very high, so that an operation like CLZ would significantly reduce the speed of zero-knowledge proof of circuits. Since CLZ is a very common bottom function, it is widely used in mathematical libraries, compressed algorithms, bits, signature schemes and many encrypted or data-processing tasks, a faster and more economical method of calculation is needed in the fare。
EIP-7939 solved this problem by introducing a new code called CLZ (0x1e). This operation code reads a 256-bit value from the stack and returns the number of lead zeros. If the number is zero, the code returns 256 because a 256-bit zero has 256 lead zeros。
This is consistent with the way CLZ works in many CPU structures such as ARM and x86, where CLZ operations are home-grown. Adding CLZ would significantly reduce the costs of many algorithms: InWad, PowerWad, LambertW, various mathematical functions, bytes comparison, bitmap scans, call data compression/decompression, and later quantum signature programs can all benefit from faster first-line zero detection。
CLZ has a gas cost set at 5, similar to ADD and slightly higher than the previous MUL price, to avoid the risk of a denial of services (DoS) attack due to low pricing. The baseline test showed that CLZ calculated approximately the same amount as ADD and that in the PSP1 rv32im certifying environment, CLZ actually cost less than ADD, thereby reducing the cost of zero proof of knowledge。
EIP-7939 IS FULLY BACKWARD COMPATIBLE AS IT INTRODUCES A NEW CODE OF OPERATION AND DOES NOT MODIFY ANY EXISTING BEHAVIOUR。
In general, EIP-7939, by adding a simple and efficient language that is already supported by a modern CPU, makes it faster, cheaper and more friendly to developers - to reduce Gas costs, to reduce byte code size and to reduce the zero-knowledge proof costs of many common operations。
Prior to this EIP, the digital signature created using the secp256r1 (P-256) curve is verified in a way that is not safe, original。
This curve is the standard used for modern devices such as Apple Security Enclave, Android Keystore, HSM, TEE and FIDO2/WebAuthn security keys. In the absence of such support, applications and wallets cannot easily be signed safely using equipment-level hardware. There had been a previous attempt (RIP-7212), but it had two serious security gaps, which were related, respectively, to a comparison of remote processing and erroneous signatures. Those problems could lead to errors in validation and even to failure of consensus。EIP-7951 REHABILITATED THESE SECURITY ISSUES AND INTRODUCED A SECURE, ORIGINAL PRE-CIRCULATION PROCESS THAT WILL EVENTUALLY ENABLE THE ETHER WORKSHOP TO SUPPORT SIGNATURES FROM MODERN HARDWARE SAFELY AND EFFICIENTLY。
EIP-7951 Adds to the address 0x100 a new pre-compilation contract called P256VERIFY, which uses secp256r1 curves to authenticate ECDSA signatures. This makes signature authentication faster and less costly than achieving it directly in Solidity。
EIP-7951 also defines strict input certification rules. If anything is not valid, pre-compilation will go back to failure and will not roll back, consuming the same Gas as the successful call. Validation algorithm follows standard ECDSA: it calculates s−1 mod n, re-establishs the signature point R', and lasts if R's rejection is endless, checks whether the x coordinates of R' match r (mod n). This corrects the error in the RIP-7212, where the RIP-7212 directly compares the r' instead of simplizing the n first。
The Gas cost of this operation is set at 6900 Gas, which is higher than version RIP-7212, but is consistent with the actual performance benchmark certified by secp256r1. Importantly, the interface is fully compatible with the Layer 2 network that has been deployed (the same address and the same input/output format) and therefore the existing smart contract will continue to function without any change. The only difference is the amended behaviour and higher Gas costs。
From a security point of view, EIP-7951 reverted to the correct behaviour of ECDSA, eliminating the issue of plasticity at the pre-compilation level, leaving the option to the application, and making it clear that pre-compilation does not require constant time execution. The secp256r1 curve provides 128 bits of security and has gained extensive trust and analysis, so it can be safely applied to the Etherpo。
IN SHORT, EIP-7951 AIMS TO SECURE THE INTRODUCTION OF MODERN HARDWARE-SUPPORTED AUTHENTICATION INTO THE INN, TO REPAIR THE SECURITY OF EARLY PROPOSALS AND TO PROVIDE A RELIABLE AND STANDARDIZED WAY OF AUTHENTICATING P-256 SIGNATURES THROUGHOUT THE ECOSYSTEM。
The table below summarizes which changes to the different Fusaka EIP are required by the Taifeng client. The check mark on the consensus client indicates that the EIP needs to update the consensus layer client, while the check mark on the execution client indicates that the upgrade affects the executive level client. Some EIPs need to update the consensus and implementation layers simultaneously, while others need to update only one of them。
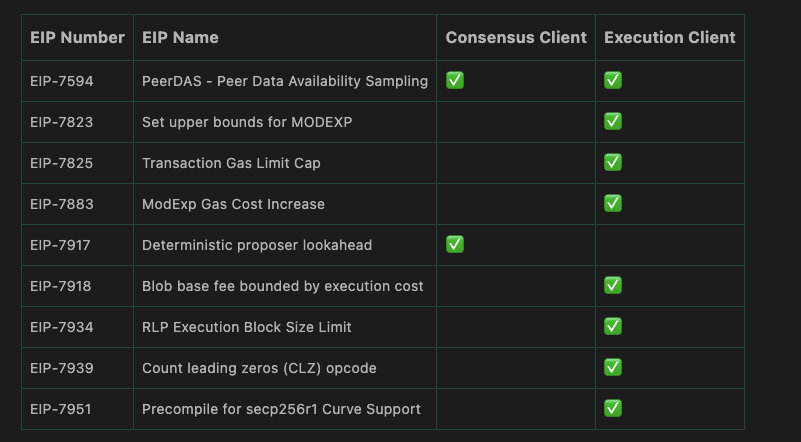
All in all, that's the key EIP that's contained in Fusaka's hard fork. Although the upgrade involved consensus and implementation of several client improvements, from Gas adjustments and upgrades to new pre-compilation, the core of the upgrade was PeerDAS, which introduced point-to-point data availability sampling, allowing for more efficient and decentrized processing of Blob data across the network。